A major Iranian cyber-attack operation against Israel and various other targets in the Middle East was revealed over the weekend.
According to the Israeli cybersecurity company ClearSky, who uncovered the ongoing cyber-attacks, the main goal of the attackers was “espionage or other nation-state interests,” Army Radio reported.
Hackers attacked 40 targets in Israel and 500 worldwide. Using classic techniques such as phishing – creating a false web page that imitates a real one to gather information – hackers targeted retired IDF generals, researchers in academia, and employees of various security firms.
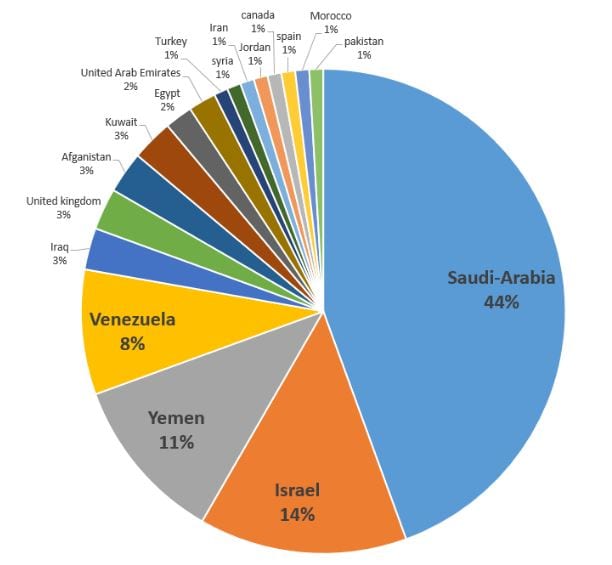
Approximately 44 percent of the attacks targeted Saudi Arabia, 14 percent targeted Israel and 11 percent targeted Yemen.
ClearSky officials confirmed that high level targets outside of Israel included the computer of a finance minister of a Middle Eastern country, human rights activists, journalists, and Qatar’s embassy in Britain.
“The targets come, mostly, from the following fields: Both Academic researchers and practitioners in the fields of counter-terror, diplomacy, international relations, Iran and Middle East, and other fields, such as Physics; Security and defence; Journalists and Human rights activists,” the ClearSky report stated.
The cybersecurity firm estimates that this particular wave of Iranian cyber-attacks began at least since July 2014 but could have started as far back as 2011. Hackers sent malware as email attachments and used advanced social-engineering techniques to infiltrate email account, telephone lines and Facebook.
“The campaign includes several different attacks with the aim of taking over the target’s computer or gain access to their email account,” ClearSky stated. “We estimate that this access is used for espionage or other nation-state interests.”
Officials at ClearSky said “several characteristics of the attacks have led us to the conclusion that an Iranian threat actor is the likely culprit.”
While the firm does not have direct evidence that Iran is behind the hacking campaign, “the context of the attacks and cover stories all revolve around Iran.”
“The attackers speak and write in native Iranian Persian and make mistakes characteristic of Persian speakers. In one of the hacked accounts, when retrieved, the interface language had been changed to Persian.”
Cybersecurity officials were able to conclude that based on the targets, victims and the fact that “the attackers only steal information,” the attackers “use the access to computers for further attacks – indicating espionage, IP theft, etc.”
ClearSky’s report comes just days after Israel was accused of being behind the Duqu 2.0 virus, which was discovered in the servers of three of the main European hotels being used to host nuclear talks between Iran and the P5+1.
Israel has denied any involvement and charges of espionage.